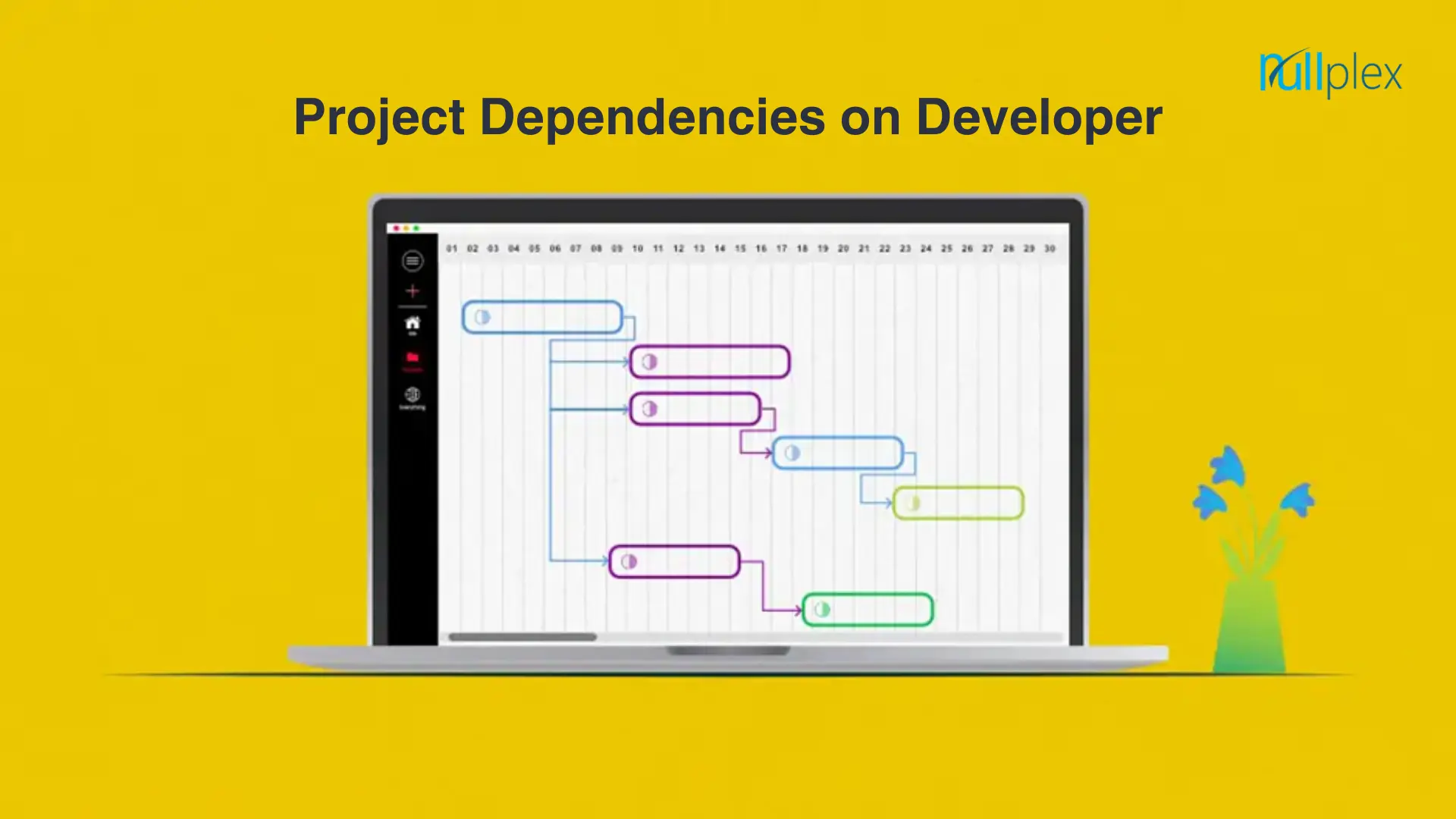
Project dependencies refer to the relationships between tasks or activities within a project, where the completion or timing of one task depends on the completion of another.
Types of Project Dependencies
- Logical dependencies
Logical or causal dependencies are quintessential to project management and cannot be avoided as they are necessary for project completion.
Tasks with logical dependencies cannot be performed simultaneously. Without completing a preceding task, the succeeding task cannot be started.
Example – You cannot publish a blog on your website straight away. It has to be written, reviewed, and edited before it is ready to be published.
- Cross-team dependencies
Cross-team dependencies are commonly witnessed in large-scale organizations where teams from different departments work together to complete a single complex project. In this case, teams depend on each other to achieve a common goal i.e. timely project completion and delivery.
- Discretionary dependencies
Discretionary dependencies, also known as preferred or soft logic dependencies, are those that are at the discretion of project teams, other stakeholders, and best industrial practices. These are not necessary for project completion but can help improve the quality of project deliverables.
- Internal dependencies
Internal project dependencies are those that project teams have complete control over and there’s no dependence on outside parties. Internal dependencies are when two tasks or activities within the same project are dependent on each other and there’s no reference to external projects and activities.
Example – The Quality Analyst team is not in a position to test software until the development process is finished.
- External dependencies
Opposite to internal dependencies, external dependencies are those when project teams have no control over external factors and are not in a position to do anything to escalate the project’s progress.
Although most project activities are controlled by internal teams. Many external factors can affect the progress of the projects such as client approval, vendors, tools, and others.
Example – A project team cannot start working on a project until the client (external party) gives the go-ahead to the team. In this case, a project team is dependent on external parties i.e. client to start working on a project.
Task dependencies in project management :
Finish to Start (FtS)
This task dependency is the most prevalent. Task A must be finished before Task B can begin.
Finish to Finish (FtF)
Before Task A is finished, Task B cannot be finished. This frequently occurs with tasks that have subtasks.
Start to Start (StS)
Task B cannot begin until Task A begins under this model. These are for tasks that need to be completed concurrently.
Start to Finish (StF)
For Task A to be finished, Task B must begin. This is crucial in circumstances where there must be overlap.
Conclusion :
Also, weekly assigned tasks will make it easier for the reviewing party to provide feedback in a more timely manner.
Weekly goals will help you focus on little portions of the projects, minuscule tasks that can be mapped out beforehand according to their urgency and priority.
These goals will help the team focus more on the task at hand. Therefore, there is no chance that they would get overwhelmed by the pressure of the upcoming tasks.